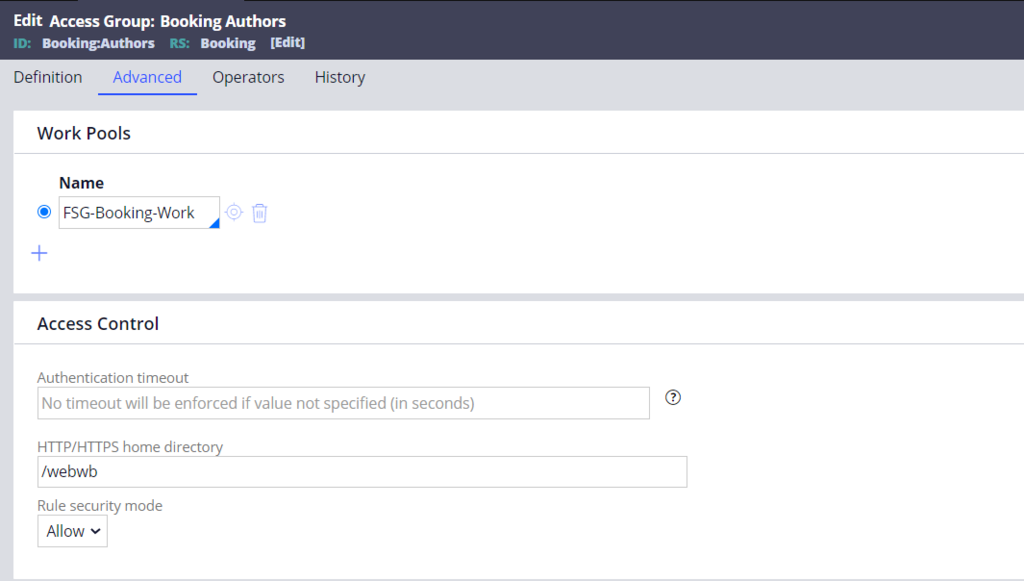
Rule security mode
The Rule security mode setting on the access group helps enforce a deny first policy. In a deny first policy, users must be granted privileges to access certain information or perform specific actions. The rule security mode determines how the system executes rules accessed by members of the access group.
The three supported rule security modes are Allow, Deny, and Warn.
Allow is the default and recommended setting. The system allows users in the access group to execute a rule that has no privilege defined or to execute a privileged rule for which the user has the appropriate privilege. If more specific security is needed for an individual rule, specify a privilege for the rule.
Use Deny to require privileges for all rules and users. This setting is recommended if only your organization's security policies require a granular and strict security definition.
If Deny is selected and a privilege is not defined for a rule, the system automatically generates a privilege for the rule and checks if the user has been assigned that privilege. The privilege is made up of <RuleType>:Class.RuleName (5)—for example, Rule-Obj-Flow:MyCo-Purchase-Work-Request.CREATE (5). The generated privilege is not added to the rule.
If the user has the generated privilege, the system executes the rule. If the user lacks the generated privilege, the system denies execution and writes an error message to the PegaRULES log.
If a privilege is defined for a rule, the system checks whether the user has the privilege defined on the rule. If not, the system checks if the user has the generated privilege for the rule. If the user has either privilege, the system executes the rule. If the user has neither privilege, the system denies execution of the rule and logs an error message in the PegaRULES log.
Use Warn to identify missing privileges for a user role. The system performs the same checking as in Deny mode but performs logging only when no privilege has been specified for the rule or the user role. The warning messages written to the PegaRULES log generate missing privileges for user roles with the pyRuleExecutionMessagesLogged activity.
Ensure sufficient time and resources are available to perform a system-wide test, including all expected users, before changing the rule security mode.
補足: The SECU0007 security alert is generated when an attempt is made to run a rule that the user is not authorized to run, and the rule security mode is set to WARN or DENY.
For more information, see the Pega Community article Setting role privileges automatically for access group Deny mode.
Check your knowledge with the following interaction:
このトピックは、下記のモジュールにも含まれています。
If you are having problems with your training, please review the Pega Academy Support FAQs.
