Authentication design considerations
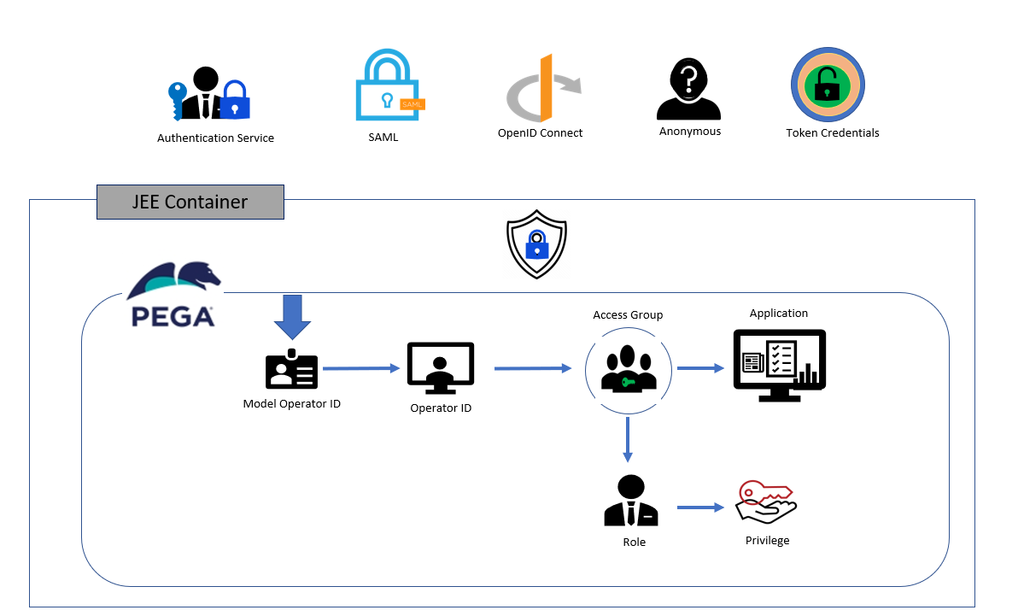
Authentication in Pega Platform™ ensures that only users and systems whose identity has been verified can access your applications. Each organization has policies on how users are authenticated on the application. Most organizations use some form of single sign-on (SSO). If the organization runs an enterprise-tier deployment, it might use container-based authentication or JAAS or JEE security. If so, this setup affects how you design your authentication scheme and your application.
The Pega application implements the organization's authentication policy. For more information on authentication protocols supported by Pega, see the Pega Community article Authentication in the Pega Platform and the help topic Authentication services.
Pega uses Basic credentials and supports Anonymous, Oauth2, OIDC (Open ID Connect), and Kerberos.
Pega can act as the Identity Provider (IdP), or the IdP can be external. An example of an external Identity Provider is Microsoft’s Active Directory Federated Service (ADFS), which is used on-premise and within Microsoft’s Azure cloud offering.
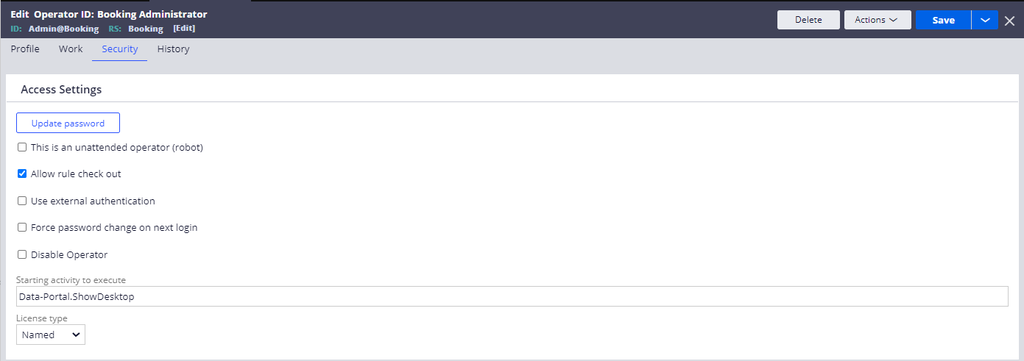
Pega is the IdP when the Authentication Type used to access Pega is Basic credentials. To enable access to Pega this way, on the Security tab of the user's operator record, clear the Use external authentication check box.
If you are having problems with your training, please review the Pega Academy Support FAQs.
Want to help us improve this content?